 The Guardian reported on another major revelation of U.S. government surveillance thanks to the leaks of Edward Snowden. The National Security Agency (NSA) is not just maintaining a database of phone numbers when people make calls throughout the world; they also are tracing every activity and communication done on the Internet. Snowden claims that the NSA routinely captures emails, browsing histories, chats, and social media communication with no warrants or court authorization to do so. He said that when he was working at the NSA he could tap into information from anyone from his computer and access real time and historical data. Even political leaders would not be immune from the NSA’s XKeyscore surveillance.
The Guardian reported on another major revelation of U.S. government surveillance thanks to the leaks of Edward Snowden. The National Security Agency (NSA) is not just maintaining a database of phone numbers when people make calls throughout the world; they also are tracing every activity and communication done on the Internet. Snowden claims that the NSA routinely captures emails, browsing histories, chats, and social media communication with no warrants or court authorization to do so. He said that when he was working at the NSA he could tap into information from anyone from his computer and access real time and historical data. Even political leaders would not be immune from the NSA’s XKeyscore surveillance.
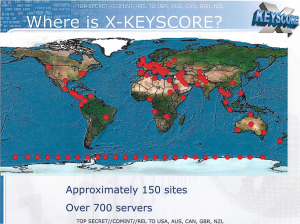
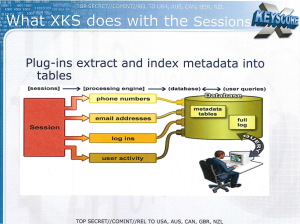
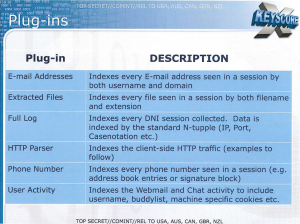
According to a top secret NSA presentation on the system from 2008, which Snowden also released, XKeyscore can provide “real-time target activity” and it stores “full-take data at the collection site”. This operation is not just U.S. based, but it includes a massive distributed Linux cluster of computer surveillance sites at over 150 locations on six continents, and it has over 700 servers worldwide. These numbers are likely considerably larger today. The system is constantly processing phone numbers, email addresses, user logins, and user activity on the web and creating a database containing metadata and full log data for either shallow or deep surveillance purposes. The monitoring of Internet users includes webmail and chat activity, which also consists of any usernames, buddylists, cookies, etc. The system also uses algorithms to establish normal activity that then can be used to detect any anomalies, which can indicate threats, such as terrorist communications or criminal activity.
According to NSA documents, becoming a target of XKeyscore can be as simple as speaking a language on the Internet that is out of place for your IP location. For instance, emailing someone in Arabic from an English speaking country likely would be flagged as suspicious. Also, if you happen to transmit encrypted files or are browsing the Internet using an encrypted browser like Tor; these activities could get attention from the surveillance network. Finally, if you search for suspicious stuff or anything considered politically incorrect or dangerous, the XKeyscore network will surely be watching and capturing the data.
 The XKeyscore system also can find specific targets if the right search terms are used. What is needed to drive down deeper is what the NSA calls a “strong selector”, which sifts through the mountains of data to find the proverbial needle in a haystack. So while it is not possible today to find everyone transmitting an encrypted document in real time, it is possible to find a certain transmission from an specific region or city which occurred during a certain time frame. For instance, the NSA presentation uses as an example: “My target speaks German but is in Pakistan—how can I find him?” Only the XKeyscore system is capable of doing this type of search and captures the data necessary to process it.
The XKeyscore system also can find specific targets if the right search terms are used. What is needed to drive down deeper is what the NSA calls a “strong selector”, which sifts through the mountains of data to find the proverbial needle in a haystack. So while it is not possible today to find everyone transmitting an encrypted document in real time, it is possible to find a certain transmission from an specific region or city which occurred during a certain time frame. For instance, the NSA presentation uses as an example: “My target speaks German but is in Pakistan—how can I find him?” Only the XKeyscore system is capable of doing this type of search and captures the data necessary to process it.
In attempting to put a positive spin on the surveillance storm surrounding this revelation, the NSA claims that by 2008 over 300 terrorists had been captured by intelligence generated by the XKeyscore surveillance system. They also claim that the system does not involve the monitoring of U.S. citizens; however, we can’t put too much reliance on that statement, because the NSA was recently caught lying about even monitoring the phone calls of Americans.
The XKeyscore system is another major effort by the government to build a global monitoring and control state. The U.S. and other countries are cooperating to create an electronic surveillance grid that can track and find every citizen no matter where they go and what they do. No doubt that when the Utah data center construction is complete, the storage capacity of the facility will be loaded with every bit of digital XKeyscore data that they can collect on all of us.
 The Bible predicts that an empire will arise at the end of the age, which will be ruled by an evil leader who will attempt to mark every person on the right hand or forehead. Revelation chapter 13 says that anyone who refuses the Mark of the Beast will not be able to buy or sell and thus they will be essentially banned from society. We now can see how the empire is preparing for this identifying mark by developing the computer and surveillance systems needed to track every human being on planet Earth. Bible prophecies are coming true before our very eyes!
The Bible predicts that an empire will arise at the end of the age, which will be ruled by an evil leader who will attempt to mark every person on the right hand or forehead. Revelation chapter 13 says that anyone who refuses the Mark of the Beast will not be able to buy or sell and thus they will be essentially banned from society. We now can see how the empire is preparing for this identifying mark by developing the computer and surveillance systems needed to track every human being on planet Earth. Bible prophecies are coming true before our very eyes!
References
1. Glenn Greewald, XKeyscore: NSA tool collects ‘nearly everything a user does on the internet’, The Guardian, Wednesday, July 31, 2013 (http://www.theguardian.com/world/2013/jul/31/nsa-top-secret-program-online-data )
2. The Guardian, XKeyscore presentation from 2008, Wednesday, July 31, 2013 (http://www.theguardian.com/world/interactive/2013/jul/31/nsa-xkeyscore-program-full-presentation )
3. NSA, XKeyscore press release, July 30, 2013 (http://www.nsa.gov/public_info/press_room/2013/30_July_2013.shtml )
Subscribe to End Times Truth
Subscribe to get notified when new articles or posts are uploaded. Always keep updated on the latest news in End Times prophecy!


